What Is The Use Of Hashcat In Kali Linux?
As of now, hashcat can support CPUs, GPUs, and other hardware accelerators on Linux, and is capable of supporting distributed password cracking with its support of CPUs, GPUs, and other hardware accelerators. MD5, HMAC-MD5, SHA1, HMAC-SHA1 and MySQL323 are some hash algorithm examples.
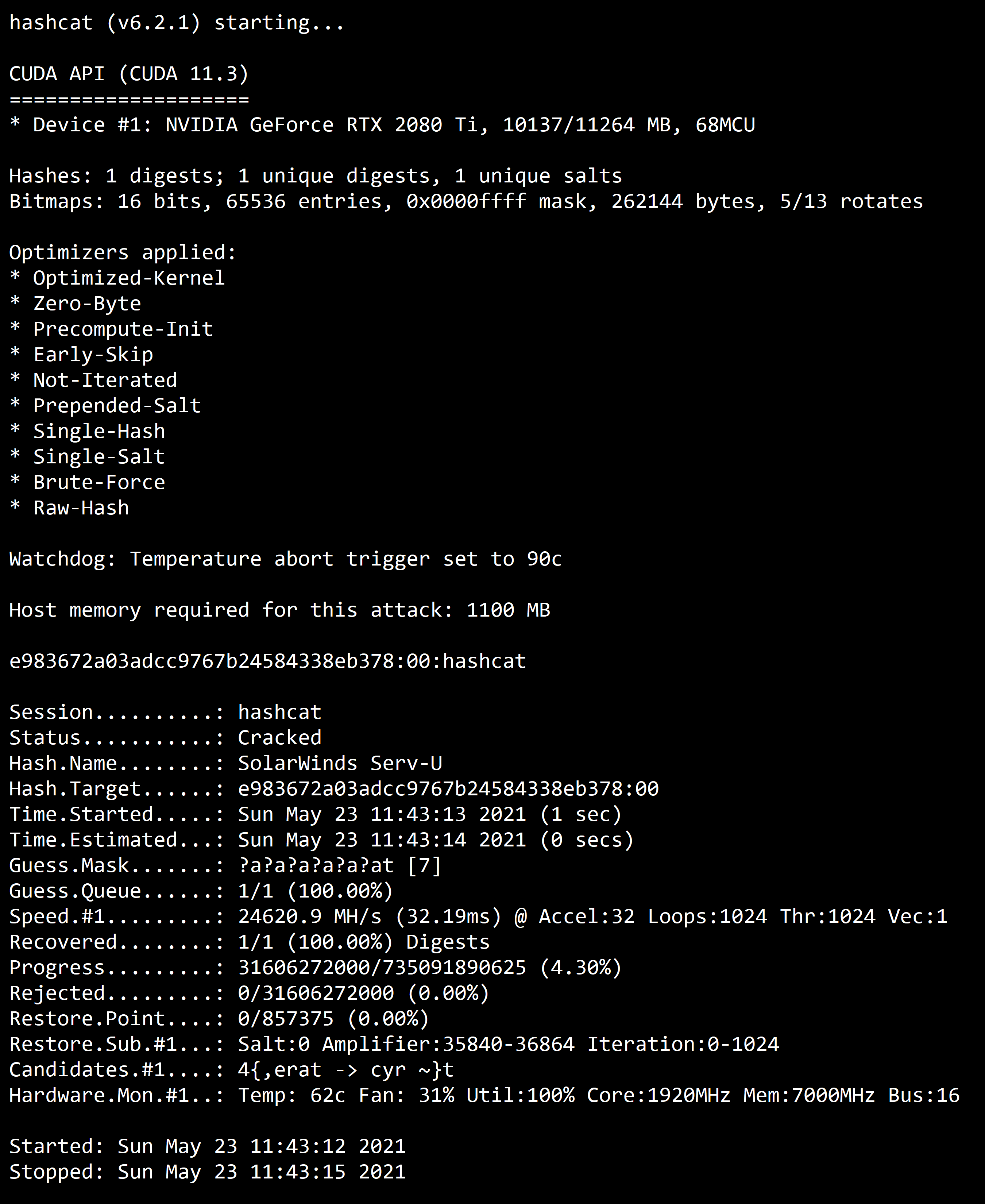
Screenshot
Is Hashcat Safe To Use?
Penetration testers uncover security holes under contract to be used by customers to improve security, which make this a perfectly legitimate enterprise choice. hashcat is used by both illegal attackers and legitimate defenders, which should be a bit more clear.
What Hashing Algorithm Does Kali Use?
As opposed to MD5, a security algorithm produces a 160-bit output with no 128-bit output to safeguard against a breakdown. There is the risk of dangerous collisions of MD5 and SHA-1, which lead to SHA-2 being the safer and more robust version of hashing.
What Is Hash In Kali Linux?
With Hashrat you get hash generators for the md5, sha1, sha256, sha512, whirlpool, jh-244, jh256, jh384 and jh-512 functions as well as HMAC versions. A word can be interpreted in any of the following formats: uppercase, lower case, decimal, hexadecimal, or base64.
The simplest way to crack a hash is to try first to guess the password. Each attempt is hashed and then is compared to the actual hashed value to see if they are the same, but the process can take a long time.
Dictionary and brute-force attacks are the most common ways of guessing passwords. These techniques make use of a file that contains words, phrases, common passwords and other strings that are likely to be used as a viable password.
It should be noted that there is no guaranteed way to prevent dictionary attacks or brute-force attacks.
Other approaches used to crack passwords:
- Lookup tables: Hashes are pre-computed from a dictionary and then stored with their corresponding password into a lookup table structure.
- Reverse lookup tables: This attack allows for a cyber attacker to apply a dictionary or brute-force attack to many hashes at the same time without having to pre-compute a lookup table.
- Rainbow tables: Rainbow tables are a time-memory technique. They are similar to lookup tables, except that they sacrifice hash cracking speed to make the lookup tables smaller.
- Hashing with salt: With this technique, the hashes are randomized by appending or prepending a random string, called a “salt.” This is applied to the password before hashing.
Cracking passwords with Hashcat
Hashcat can be downloaded here. It can be used on Kali Linux and is pre-installed on the system. It possesses the following features:
- It is multi-threaded
- It is multi-hash and multi-OS based (Linux, Windows and OSX native binaries)
- It is multi-Algorithm based (MD4, MD5, SHA1, DCC, NTLM, MySQL, etc.)
- All attack modes can be extended by specialized rules
- It is possible to resume or limit sessions automatically. They recognize recovered hashes from the outfile at startup
- It can load the salt list from the external file. This can be used as a brute-force attack variant
- The number of threads can be configured and executed based on the lowest priority
- It supports both hex-charset and hex-salt files
- The 90+ algorithms can be implemented with performance and optimization in mind
A small laboratory setup of how to crack a password is presented in the next section. A dictionary attack will be simulated for a set of MD5 hashes initially created and stored in a target file. The “rockyou” wordlist found in Kali Linux was used.
How to crack a password via a dictionary attack
1. Create a dictionary with MBD5 hashes
To start this demonstration, we will create multiple hash entries containing several passwords.
In detail, they will then be outputted to a file called “target_hashes.” Each command should be executed in the terminal, as demonstrated below:
The -n option removes the new line added to the end of “Password.” This is important as we don’t want the new line characters to be hashed with our password. The part “tr –d ‘ -‘ “ removes any characters that are a space or hyphen from the output.
2. Check password hashes
To do this, we need to type the following command line in the terminal:
This is also illustrated in the table below:
Start Hashcat in Kali Linux
Hashcat can be started on the Kali console with the following command line: hashcat -h.
This is illustrated in the screenshot below:
Some of the most important hashcat options are -m (the hashtype) and -a (attack mode). In general, we need to use both options in most password-cracking attempts when using Hashcat.
Hashcat also has specifically designed rules to use on a wordlist file. The character list can be customized to crack the password(s).
Finally, Hashcat provides numerous options for password hashes that can be cracked. This can be seen in the screenshot below:
4. Choose the wordlist
Kali Linux has numerous wordlists built right into it. To find them, use the following command line: locate wordlists
This is illustrated in the screenshot below:
The “rockyou” wordlist is now used, as illustrated below:
5. Cracking the hashes
In the final step, we can now start cracking the hashes contained in the target_hashes.txt file. We will use the following command line, as illustrated below:
- -m 0 designates the type of hash we are cracking (MD5)
- -a 0 designates a dictionary attack
- -o cracked.txt is the output file for the cracked passwords
- target_hashes.txt is our input file of hashes
- /usr/share/wordlists/rockyou.txt is the absolute path to the wordlist file for this dictionary attack
6. Results
Finally, we have cracked five out of seven target hashes that were initially proposed. These can be seen below:
These passwords are weak, and it does not take much effort or time to crack them. It is important to note that the simpler the password is, the easier it will be to detect.
Frequently Asked Questions
How do I earn money with affiliate marketing?
Who Can Be An Affiliate Marketing Program Seller?
How do I know what's popular?
How do I find products and companies to promote?
How do I promote affiliate products?
People are also reading:- Smartphone Circuit Diagram information.
- 10 Best Ethical Hacking Books for Beginner to Advanced Level. Best Online Teaching Platforms Name for Teachers
- Affiliate Marketing For Beginners to Advance Successful Strategy.
- Best Password cracking techniques used by hackers. Explanation
- How many types of darknet user software and website.
- What is PageMaker? PageMaker Introduction
- How to become an operations manager ? Build leadership skills.
- Popular Types of Information Systems and Their Applications
- Smartphone Circuit Diagram information.
- 10 Best Ethical Hacking Books for Beginner to Advanced Level. Best Online Teaching Platforms Name for Teachers
- Affiliate Marketing For Beginners to Advance Successful Strategy.
- Best Password cracking techniques used by hackers. Explanation
- How many types of darknet user software and website.
- What is PageMaker? PageMaker Introduction
- How to become an operations manager ? Build leadership skills.
- Popular Types of Information Systems and Their Applications










